
Decentralizing Identity - Taking Back Control
13 October, 2021, by Simon Young
Self-Sovereign Identity (SSI), or decentralised identity, is an emerging paradigm and offers an alternative approach to the centralised way in which identity is used today.
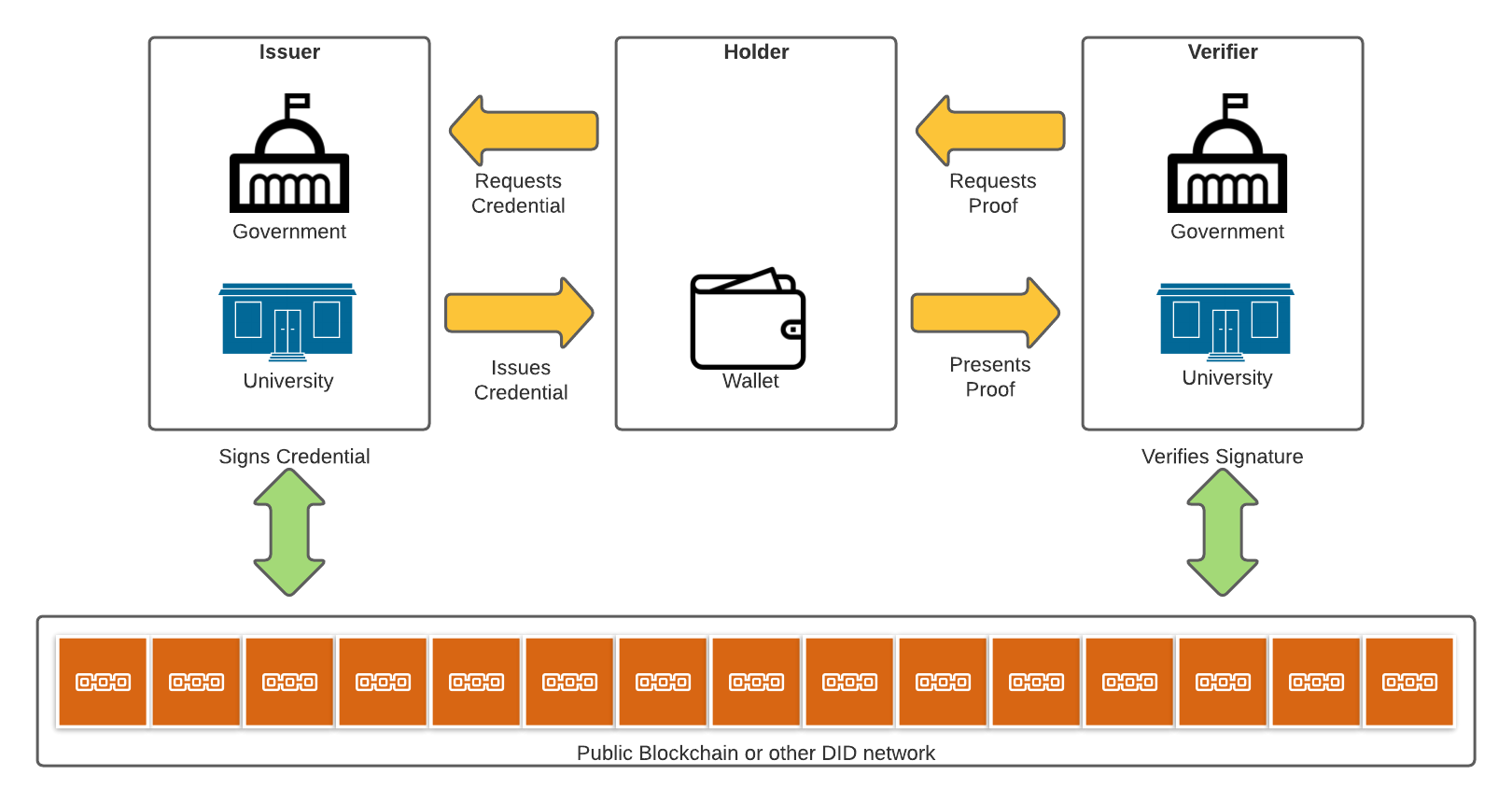
In a nutshell, Self-Sovereign Identity allows individuals to manage their own identities by moving physical credentials to digital devices. An individual will receive a credential from an issuer which will be stored in their digital wallet.
These credentials can then be presented by the holder to the verifier who can then verify them via a blockchain or other form of public ledger. The blockchain or ledger itself does not store any information about the user, just the data required to verify the credential being presented.
This decentralised approach offers individuals more independence and more privacy, something that is becoming increasingly important in a world where organisations can capture large amounts of personal and sensitive information and also where mismanagement of this data, either through breaches or selling of data is increasingly prolific.
Terminology
Credential: Generally a paper or plastic based item which is used to prove your identity. For example a passport or driving license.
Verifiable Credential: A digital version of a credential. They can be issued by anyone about anything and presented to be verified by everyone. The verifier must be able to determine who issued the credential, that it has not expired/been revoked and that it has not been tampered with.
Issuer: The source of the credential. An issuer could be an organisation such as a government agency (passport), university (degree), financial institution (credit card), company (ID card), utility company (utility bill) and so on. Individuals or even "things" can also be issuers (perhaps a device needs to digitally sign a sensor reading or audit log).
Holder: The person, organisation, device etc. that holds the credential in a digital wallet. They can present proofs of claims from one or more credentials when requested by a verifier. It is important to note that the holder always has the option to refuse the proof request.
Verifier: Any person, organisation or device ("thing") that seeks an assurance of some kind related to the subject of the credential. The verifier will request proof from a holder regarding the claims the verifier needs to validate.
Claim: A piece (or pieces) of information that some authority claims to be true about you.
Digital Wallet: Similar to a physical wallet where one may keep their driving license or credit cards. Provides a secure way to protect, store and easily access digital credentials.
Decentralised Identifier (DID): A globally unique identifier that does not require a centralised registration authority because it is registered with distributed ledger technology or other form of decentralised network.
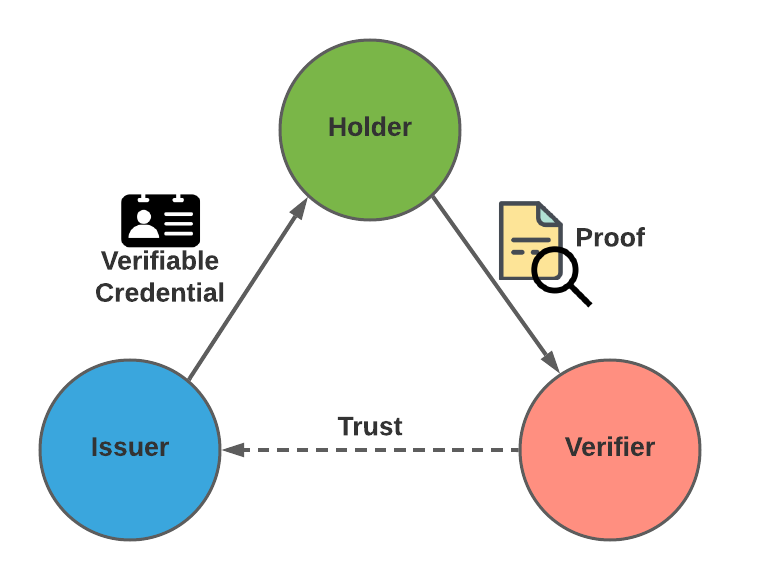
Trust
The relationship between the issuer, holder and verifier is known as the "Trust Triangle". This is simply a digital representation of how normal human trust relationships work. Just like in real life, the holder can choose which credential to present, the verifier can choose which credentials they will accept.
NOTE: There may be situations where parties will act as both holders and issuers in a single transaction!
Benefits
The benefits of SSI manifest in several ways. Many financial, political, cultural and social interactions depend on proof of identity. By moving identity to effectively require just a digital device and some sort of connection to the internet, the barriers to these interactions are more easily bridged. Both access to a digital device and availability of an internet connection are increasing, even in new or emerging economies.
- SSI reduces the proofing complexity. Each question has a simple "yes" or "no" answer.
- There is no need to store a plethora of personal information in a centralised repository. This also means that holders only need to provide the information required (selective disclosure) by the verifier and always have control over whether or not they provide the answer.
- SSI credentials are tamper-proof through the use of cryptography.
- SSI credentials can be verified anywhere and at any time.
- Personal data is not stored on any centralised server.
- The potential to secure and deactivate access based on the provisioning or revocation of a single credential.
- Audit trails improved by ensuring that modification of audit logs are tracked using immutable technologies (such as blockchains) preventing nefarious manipulation of log files by bad actors.
- Lastly, they are a way of reducing the need for passwords, you only need to remember the password to your wallet!
