
Is It Time You Upgraded Your Access Management Solution?
22 September, 2021, by Natasha Free
If I were a betting woman, I would wager that there are a large number of organisations out there who would not like to admit that their access management solution is somewhat outdated. Unless they have deep pockets or corporate compliance drivers, the chances are that upgrading their access management solution has latterly looked either too difficult or too expensive.
The good news is that access management technology has come on in leaps and bounds and upgrades or migrations don't need to be either painful or budget-busting anymore. There have been improvements in the security of these systems, as well as usability, orchestration, and compliance & reporting.
Modern Single Sign-On (SSO)
Focus has shifted towards “everywhere operations” at the same time as the number and type of users has increased significantly. What if you could consolidate your access management needs into one single, central control layer? One tool to manage all access and authentication requests, coupled with a policy engine enabling a policy-based approach to access management?
The use of open standards means that you can manage access to new cloud-native apps alongside access to legacy on-premises apps all from the comfort of a single pane of glass.
This is an important first step to moving away from siloed solutions and retiring legacy ones that have outlived their usefulness. Indeed, with more and more cloud native applications and the need for a seamless user experience, having a legacy access management tool could in fact be detrimental to both productivity and security.

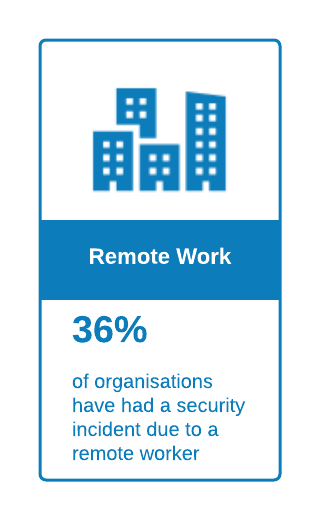
Legacy access management solutions are not suited to managing the new remote workforce, disparate user types, or the Cloud First approach to systems' procurement that is prevalent in today's enterprises. Access management needs to be updated in order to enable the more rapid changes to services required by businesses today.
Improved UX
The nexus between better security and user experience has always been tricky. Too loose? You risk security. Too tight? You risk user backlash, or worse, user circumvention of your carefully planned security measures!
In addition to enabling seamless SSO, you can now leverage adaptive access capabilities. The information you have about the user, their location, the device they are using and even the manner with which they use your application can be used to apply policy based access control at run-time. Additional authentication challenges can be configured depending on criteria aligned to business policy and processes. Individually tailored user journeys are now a reality and are a welcome step towards a truly 'frictionless' user access journey.
Compliance
Is compliance a significant driver for your business? Modern access management tools are very flexible and adaptive in this respect and should enable you to implement authentication and authorisation policies that align with your particular compliance drivers. Combined with a complementary identity governance tool, the reporting and recertification possibilities are numerous and will also put you in a good place to handle new and increasing requirements around user privacy, preferences, and consent management. Those requirements can now be satisfied regardless of the physical location of your various user communities and the subtle differences in jurisdictive legislation they may face.
Orchestration
Modern access management tools can enable a faster time to user access as well as ensuring access to the right applications. There is a greater and more refined level of automation meaning you can cut down on repetitive administrative tasks (and their associated cost). Gone are the days of new recruits being sent home because they can’t access the right systems on their first day. Modern access management solutions have been shown to enhance productivity and can speed the time to market for new digital offerings.
The Future
Access management is already more focused on an identity first approach rather than a traditional ‘secure the perimeter’ access policy, meaning that modern tools can easily fit the demands of cloud first or 'hybrid cloud' initiatives. Interesting advances are being made all the time with machine learning that will lead to improvements in data analysis and dynamic policy driven real-time decision making on access and authentication.
In order to keep up with the rapidity of changes in the way we work and consume digital products, access management tools need to be simple to implement & use, scalable and flexible. Legacy access management tools are no longer up to the job of managing access in the current era and indeed, may put organisations into a vulnerable position.
There is always room for improvement in identity and access management solutions, not least because the threat and opportunity landscape is always shifting. But the speed of change recently and the fact that many organisations are struggling to manage modern access demands using legacy tools means that upgrading your platforms can no longer wait.
The time to modernise is always now.
