
Simplify Your User Lifecycle Management
28 July, 2021, by Simon Young
Today, it is rare for an employee to not have to interface with technology in one way or another. Whether it is simply communicating via email or using an application which lets them know which parcel should be delivered next, technology is everywhere. Although these example interactions sound somewhat basic, there will be an IT account (or more) required to facilitate them.
So how do employees get assigned those accounts?
Business processes can be complicated and one of the most complicated processes can be managing a user's IT account lifecycle effectively and securely. When people join the organisation, they need accounts and access. Whilst they are with the organisation, at some point they will need to request additional access which may lead to a new account. Lastly, when they leave all that access needs to be tidied up and removed.
This can be reduced to simply CRUD, with less emphasis on the Read.
Ensuring these processes are automated, robust and as simple as possible has several benefits.
Benefit #1: Productivity
If an employee can start on day one with all the access and accounts required to perform their job function then they can start being productive straight away. If the accounts are not ready, or if the process they have to follow to attain the extra access is cumbersome, then the new starter will not be left with the best impression.
This productivity extends past the end user. If Human Resources or the Line of Business manager have to raise multiple forms and get various approvals to get the new starter the access, then their productivity (and perhaps sanity) will also be impacted.
This will be exacerbated during periods of high intake, for example the onboarding of seasonal or otherwise temporary workers. Another downside to manual processes is that they also introduce dependencies on various members of staff which can lead to mistakes, other errors, or simply not being fulfilled in time.
Benefit #2: Security
Automating the Joiner, Mover, Leaver (JML) processes or delivering self service access request capability increases the security posture.
Having a good grasp on job functions and the access required to support those functions can enable a business to automate the process of entitlement assignment. Tagging entitlements as "birthright" entitlements means that when a user joins the organisation or moves to a different department, they can be automatically granted a defined set (and only that set) of entitlements. Moreover, any entitlements they may have previously had whilst working in a different department can be automatically removed.
Benefit #3: Audit Trails
Having a repeatable and approval based process ensures that there is an audit trail of the request, from whomever raised the request, whomever approved (or did not approve) the request and when the request was fulfilled.
Closing The Loop
The lifecycle of a user within a business certainly needs to support Joiner, Mover and Leaver actions. But to close the loop, we also need to consider re-hire policies, and validation of the entitlements assigned.
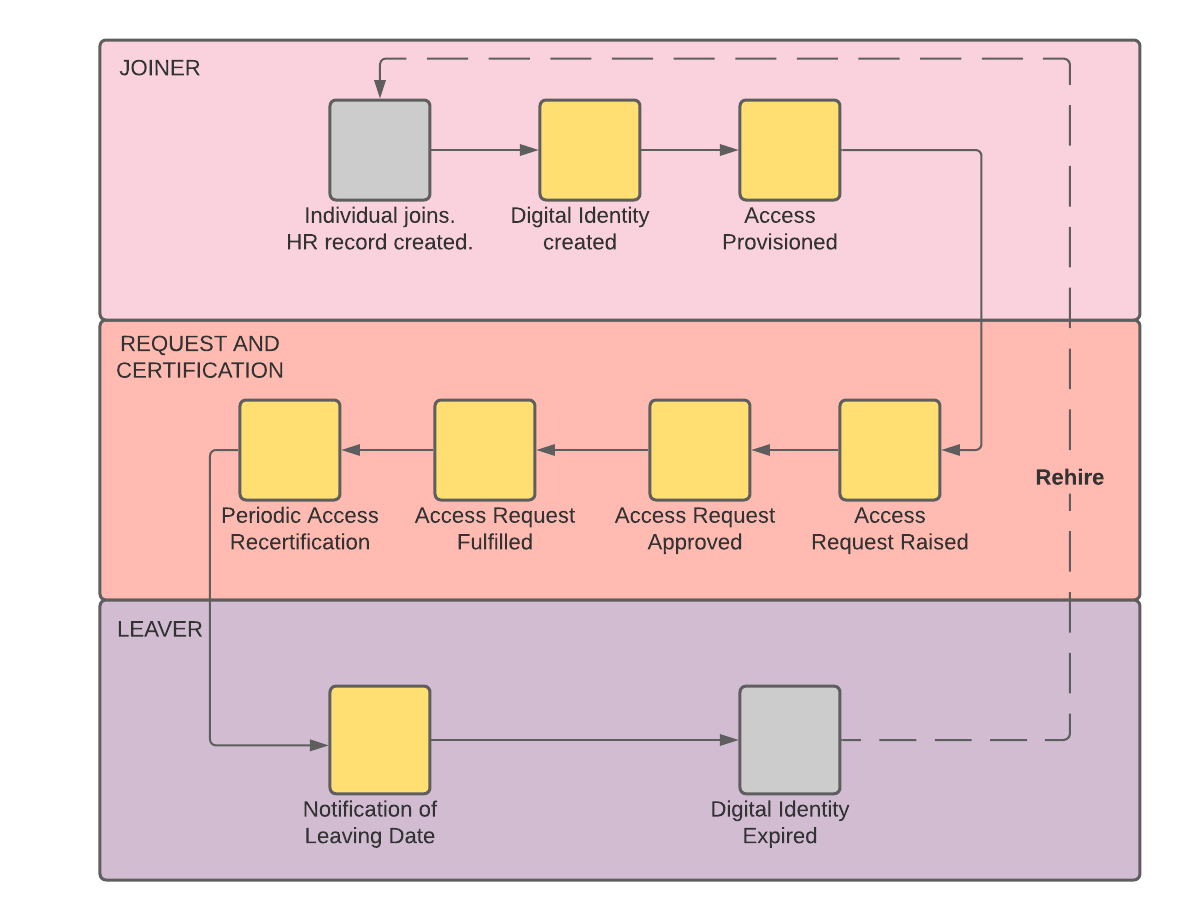
Regular certifications of access rights are a requirement in almost all organisations. In theory, re-certifying access will ensure that only the access a user needs to perform their job is assigned and any superfluous access is removed.
These reviews can be broken down in many ways, such as per user, per account, per application and so on. Aside from the importance of ensuring access is reviewed, this is great way to demonstrate to an auditor that you have sufficient controls in place, both with the process of granting access but making sure that over time access is removed when it is no longer required.
Contact us for more information on how you can best simplify your user lifecycle.
